In this short tutorial I will explain how to run a Docker container with GPU support. This becomes important if you want to run AI applications such as the Imixs-AI project with Docker. My tutorial is based on Debian 12 (Bookworm) and the usage of a NVIDA graphic card. I assume that you already have installed Debian and the Docker engine. Read the official install guide about how to install the Docker engine on Debian.
Continue reading “How to Run Docker with GPU Support”BPMN 2.0 and Jakarta EE – A Powerful Alliance
A BPMN Workflow engine based on the Jakarta EE Framework forms a powerful and effective combination for developing enterprise applications with a focus on business process management. Both, Jakarta EE and BPMN 2.0 are standardized and widely supported. The scalability of Jakarta EE provides a secure foundation for building enterprise applications with robust business process management capabilities. This enables developers to leverage the strengths of both technologies to create efficient, interoperable, and maintainable BPM solutions. In the following I will explain the aspects in more detail.

New Version of Open-BPMN Available!
Today we released the latest Version of Open-BPMN. The new version includes a lot of enhancements and new additional features. This makes it more easy to model BPMN Diagrams:
- Improved Layout
- Property Panel can be opened by double click
- BPMN Pool and Lane Design improved
- Fixed minor layout issues
Open BPMN can be run in a Browser or installed on Microsoft VS-Code. You can install Open-BPMN form the VS–Code Marketplace.
BPMN 2.0 Extensibility Mechanism
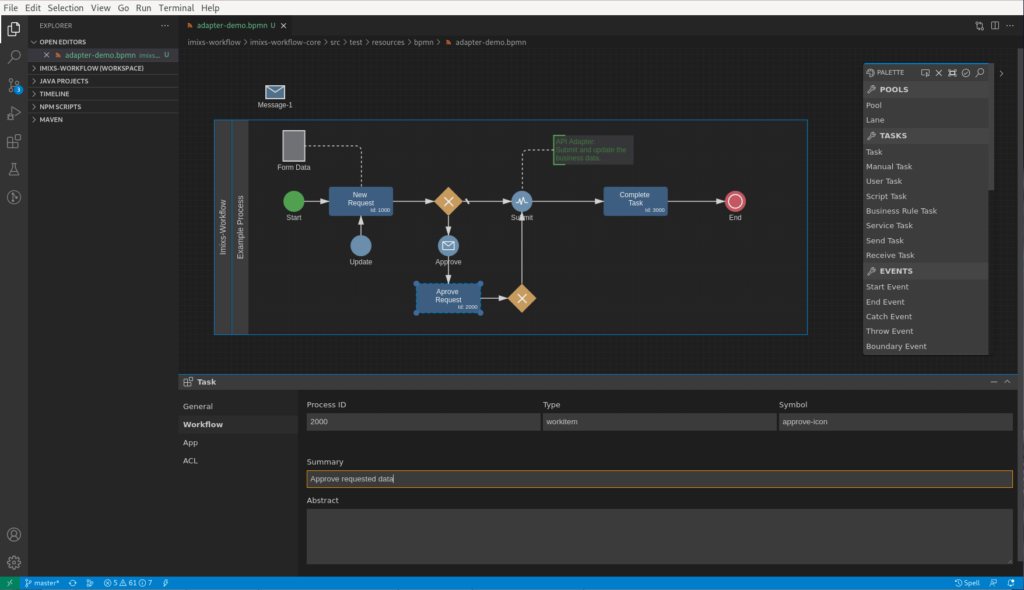
One of the core features is the extensibility of Open BPMN. Open-BPMN enables you to customize it’s behavior and appearance by adapting the BPMN 2.0 extension mechanism. This extension mechanism can be used to adapt BPMN elements to the unique requirements of a vertical domain, and still have a valid BPMN Core. Open Source Workflow Engines like Imixs-Workflow already integrate Open BPMN into there tooling platforms.
But more important, Open-BPMN is based on the Eclipse Graphical Language Server Platform (GLSP). This platform provides a huge set of features and an API to extend and adapt the Modeler in various ways.
How to Build Good Workflow Applications
In this short tutorial I will explain a few basic design patterns helping you to build really good Business Process Management Systems based on Imixs-Workfow. For these patterns it does not matter if you build a app just with the Imixs-Workflow core engine or if you use Imixs-Office-Workflow. All patterns explain very basic concepts which will help you a lot in understanding to build and maintain your business application. So lets start!
Continue reading “How to Build Good Workflow Applications”Open-BPMN for Visual-Studio Code
Today we released version 1.0.0 of Open-BPMN for Visual Studio Code.
Open BPMN is a free and open modeling platform to create and maintain business models based on the BPMN 2.0 standard. Open BPMN can be used by business analysts to design a top level business process, as also by architects and developers to model the technical details of complex processing logic. Further more, Open BPMN provides an extension mechanism to adapt the modeling platform to the individual requirements in any business process project.
Open-BPMN can be installed from the VS-Code Marketplace or as VSIX extension.
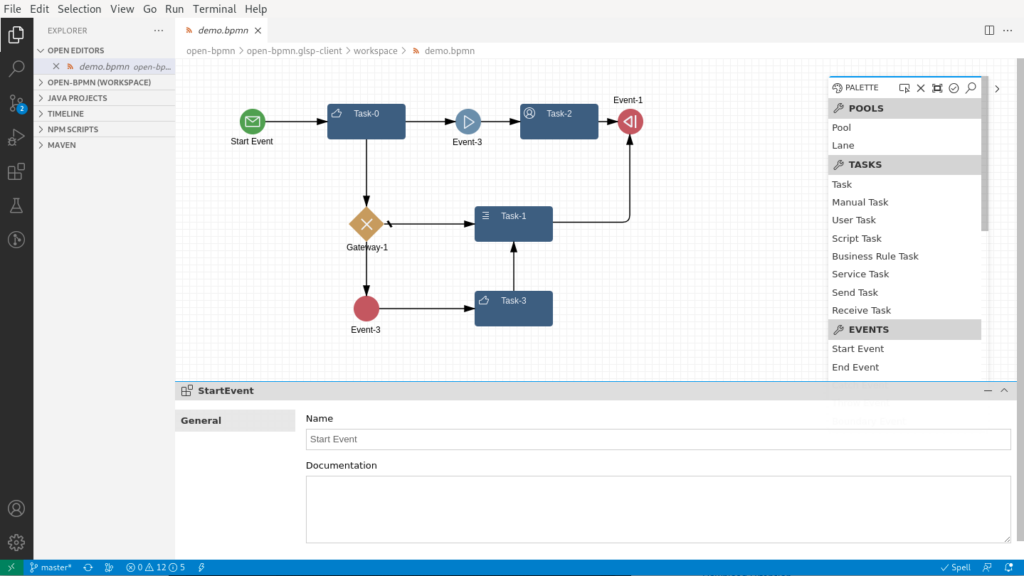
The goal of this project is to provide an open and extensible graphical BPMN modelling framework for an agile and innovative community around the BPMN standard.
Extensibility
BPMN 2.0 introduces an extensibility mechanism that allows extending standard BPMN elements with additional properties and behaviour. It can be used by modeling tools to add non-standard elements or Artefacts to satisfy a specific need, such as the unique requirements of a vertical domain, and still have a valid BPMN Core.
One goal of Open BPMN is to not only provide a graphical modeling tool, but also to allow developers and independent projects to easily customize the behaviour and appearance of the editor for specific BPM workflow engines that use this BPMN 2.0 extensibility mechanism.
Open Source Workflow Engines like Imixs-Workflow integrate Open BPMN into there tooling platforms and extend the core features of BPMN 2.0 with platform specific functionality.
BPMN Modelling with Eclipse GLSP

Imixs-Workflow started a new modelling project called Open-BPMN. Open-BPMN is a free BPMN 2.0 modelling platform that can be extended and customized by any BPMN 2.0 compliant execution engine. The primary goal of this project is to provide a graphical BPMN editing framework that can be extended in various ways by different solutions to create an agile and innovative community around the BPMN standard.
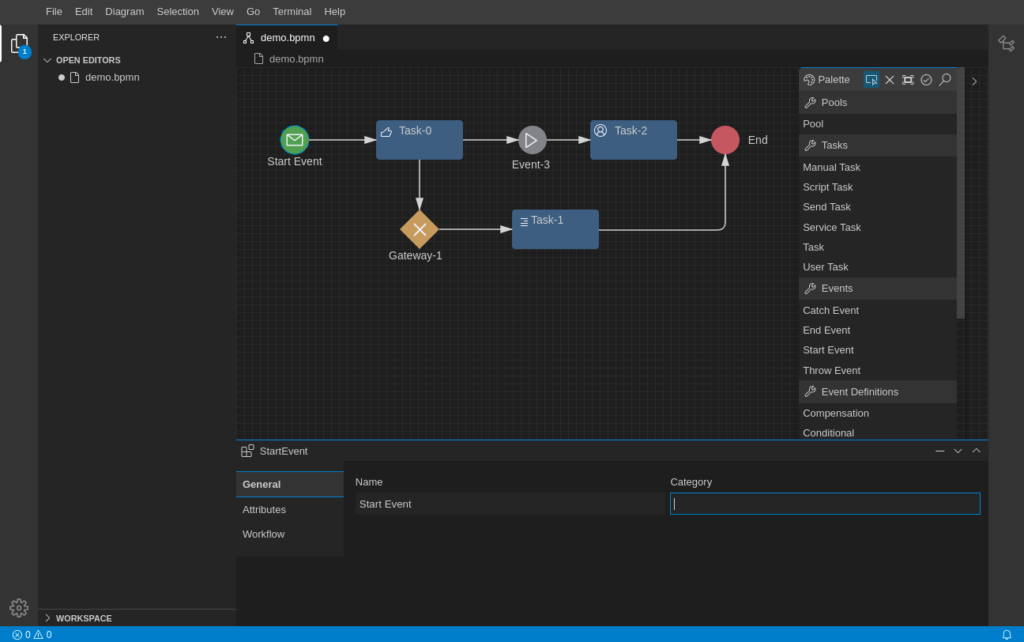
For this reason we build Open BPMN based on the Eclipse Graphical Language Server Platform (GLSP). GLSP is an extensible open-source framework for building custom diagram editors based on web technologies. The platform provides a language server protocol (LSP) for diagrams that allows to adapt any kind of modelling language. GLSP splits into a server part and a client part. The server part is responsible to handle the underlying model stored in a filesystem, database or microservice and provides the graphical model meta data. The client part communicates with the server and provides the graphical representation and the modelling tools to create and modify a model.
The main advantage of GLSP is its openness and extensibility. In this way it allows us to not only provide a new flexible BPMN modelling tool but also adapt the BPMN Extensions of Imixs-Workflow within this solution. Adapting the Imixs-Workflow engine within the Open-BPMN Modeller is a first proof of concept showing the flexibility and power of this platform.
Multi IDE Support and Extensibility
GLSP can be integrated into different IDEs like Microsoft VS Code, the web based Theia IDE and of course the Eclipse Platform. This allows us to use Open-BPMN in much more different ways and projects and opens the modelling tool to a broader community.
With the extensibility of GLSP, Open-BPMN can not only be extended within the extension mechanism of BPMN 2.0, but also by additional views, editors and UI elements in various ways. For example custom Form editors, Analyse-Panels or Reporting Tools can be adapted by individual projects.
The Community
There is also a strong and agile community around this project that supports us in adapting the technology into the Imixs-Workflow project. Of course Open-BPMN is free software and we invite you to participate in it. There are different ways how you can do that. Join the Open-BPMN Project on GitHub or help us to improve the project by reporting bugs or start a new discussion.
So if you plan to customize BPMN for your own software project, then join Open-BPMN and get support from an agile community. Of course, we also offer professional support for your project.
Compare Workflow Engines
The term “workflow engine” is not clearly defined in software development and therefore we would like to give a brief overview of different aspects and types of workflow engines in the following blog post.
If you take a look at the Github page awesome-workflow-engines, you will find an impressive number of open source workflow engines. But not all of these engines solve the same problem. The idea behind the term ‘workflow’ can be very different and so the functionality of a workflow engine. In general a workflow is a series of tasks or activities that are required to complete a specific process. Such a process can involve multiple people, teams, microservices or even other IT systems. Thus, it becomes clear that when comparing Workflow Engines, various aspects must be taken into account.
Continue reading “Compare Workflow Engines”New AI for Automated Document Import
The latest version 4.5.3 of our Business Process Management suite Imixs-Office-Workflow now includes an improved AI module. The system can import documents and automatically recognize and assign their content. For example, incoming invoices and delivery notes can be processed automatically in background. This significantly shortens throughput times in document based business workflows.
The open source module Imixs-ML is based on a machine learning approach in combination with pattern recognition. Good results are achieved even with small amounts of data. In addition, Imixs-Office-Workflow includes a self-learning AI system. This means that the system permanently improves its ability to recognize content from new documents in the background without having to import big training data.
After an automated document import – e.g. from an e-mail mailbox or an Office scanner – the user can check the data and correct it where necessary.
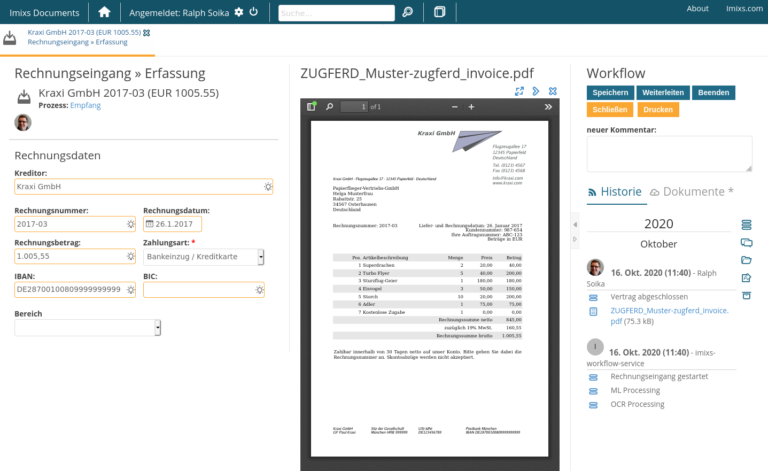
Model Your Business Process Quick & Easily
With the Imixs Workflow Technology, all kinds of business processes can be easily modelled with BPMN 2.0. Even complex approval processes like the 4-eyes principle are supported by the Imixs Workflow engine.
Due to its openness Imixs-Office-Workflow supports many open interfaces to various IT solutions and server systems. Thus, integration into an existing enterprise IT can be done very easily.
Through our consulting concept, we help companies to digitize their business processes. Get in touch with us and find out more!
Imixs-Admin Runs on Jakarta EE 10!
With our latest version 6.0.0 of the Imixs-Admin client we launched our first Jakarta EE10 project. Imixs-Admin is developed with Java 11, Jakarta EE 10 and Faces 4.0. It runs on Wildfly version 27.0.0.Alpha4.
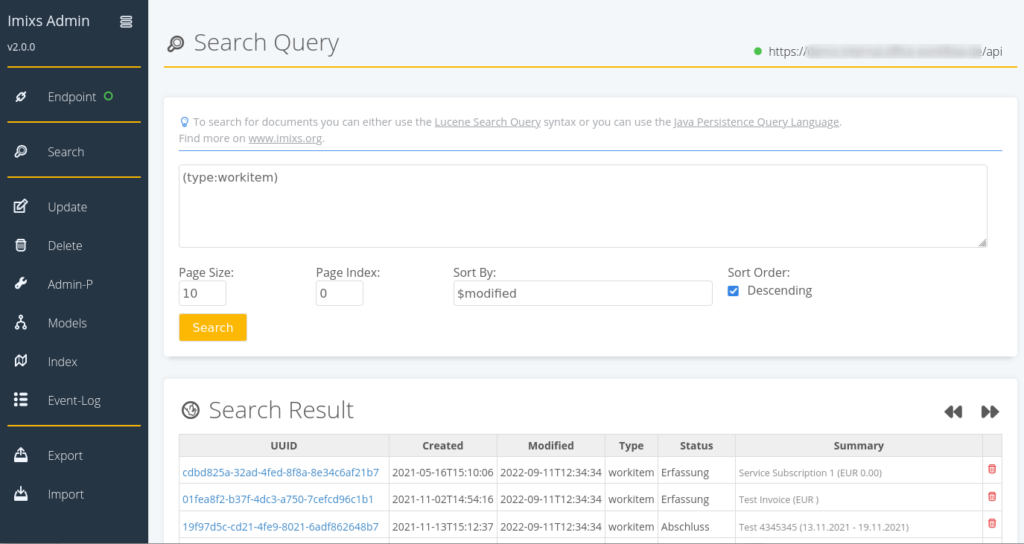
This project is a first prove of concept to demonstrate the compatibility of Imixs Workflow with Jakarta EE 10. In the course of the implementation, we also migrated the Imixs Rest Client library Melman to Jakarta EE 10.
We will soon provide our next version of Imixs-Office-Workflow – a enterprise business process management suite – running on Jakarta EE 10 too.
License Switch GPL-3.0 to EPL 2.0
We consider to switch the licence model for Imixs-Workflow from GPL-3.0 to EPL 2.0. The new license model will affect the Jakarta EE 9 development stream. Older versions of Imixs-Workflow will not be affected from this change.
The Eclipse Public License is a modern license which reflects the norms and expectations of an industry that has changed a lot in the last years. The EPL has been approved by the Free Software Foundation (FSF) and the Open Source Imitative (OSI).
As a weak copyleft license, the EPL is a middle ground of sorts between permissive options (like the MIT License or Apache License 2.0) and strong copyleft licenses (like GPL v2 and GPL v3.) A core requirement of the EPL – one that’s not part of permissive licenses – is that derivative works of EPL-licensed code must also be licensed under the EPL. As such, anyone who distributes a program that constitutes such a derivative work must also make their source code available. Find more details here.
In addition we plan that the new license will include also a secondary license for GPL-2.0+ compatibility. In this way you can still license your work under GPL if you like.
The notion of a “Secondary License” is intended to permit combining content licensed under the EPL-2.0 with an otherwise incompatible license, specifically the GNU General Public License, v2.0 or greater. This means that the content that includes a Secondary License clause may be combined with content distributed under the terms of that Secondary License, and the combined content can be then be collectively distributed under the terms of that Secondary License.
Does EPL-2.0 change the scope of the copyleft?
The EPL-2.0 is a weak copyleft license. In its simplest terms, that means that if you have modified EPL-2.0 licensed source code and you distribute that code or binaries built from that code outside your organization, you must make the source code available under the EPL-2.0.
Can I take a Program licensed under the EPL, compile it without modification, and commercially license the result?
Yes. You may compile a Program licensed under the EPL without modification and commercially license the result in accordance with the terms of the EPL.
Can I modify the EPL-2.0 License?
No. Everyone is permitted to copy and distribute copies of the new Agreement; however, in order to avoid inconsistency, the agreement is copyrighted and may only be modified by the Agreement Steward who reserves the right to publish new versions (including revisions) of this Agreement from time to time. No one other than the Agreement Steward has the right to modify the Agreement.
Find also more details see the EPL FAQs. If you have any questions please add your comments here.
